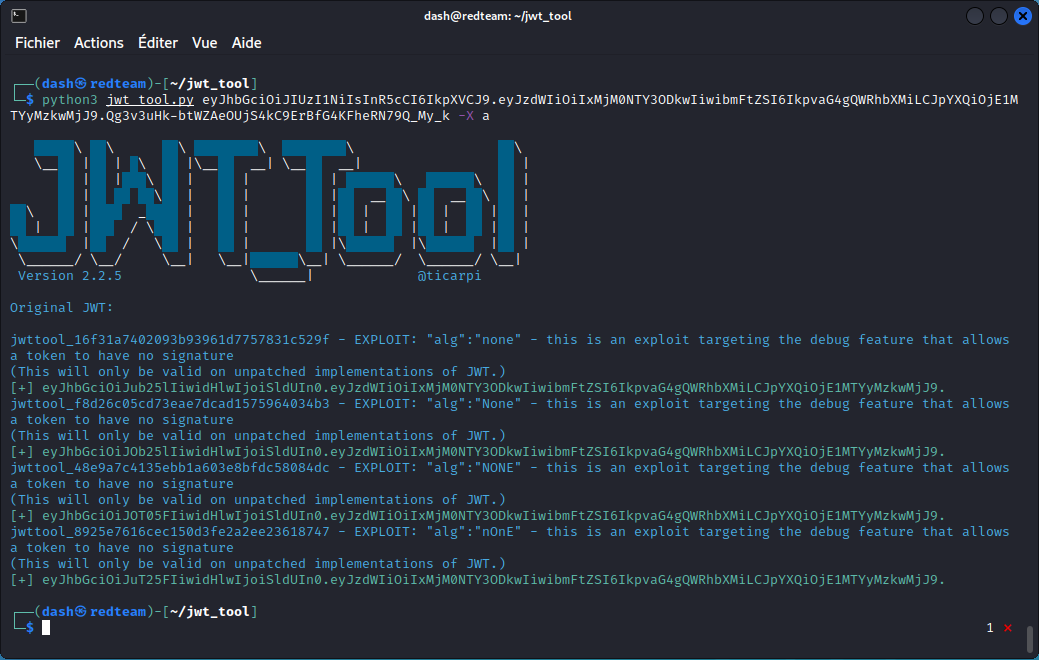
Hacking JWT Tokens: Bruteforcing Weak Signing Key (jwt_tool) | by Shivam Bathla | Pentester Academy Blog

github.com-ticarpi-jwt_tool_-_2022-09-09_11-00-12 : ticarpi : Free Download, Borrow, and Streaming : Internet Archive

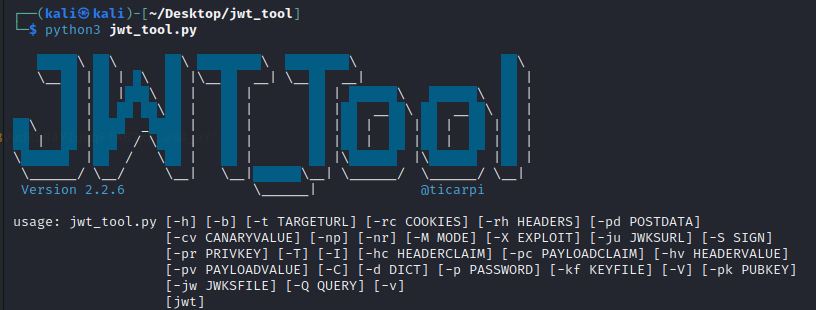
Create a hacker machine that supports Andriod, Web and API. What to install an how to install. – Tips and Tricks








![JWT Tool Attack Methods ][ ticarpi JWT Tool Attack Methods ][ ticarpi](https://www.ticarpi.com/assets/images/burp_jwt_pre.jpg)